What is social engineering?
In the context of online security, one term that keeps cropping up is social engineering. But what does it mean?
A cyber-scam designed to compromise your Internet security can comprise of both technical and non-technical approaches.
A technical approach, colloquially known as “hacking”, can include the development of malicious software (malware,) discovering programming vulnerabilities in cyber defenses or exploiting security vulnerabilities in software.
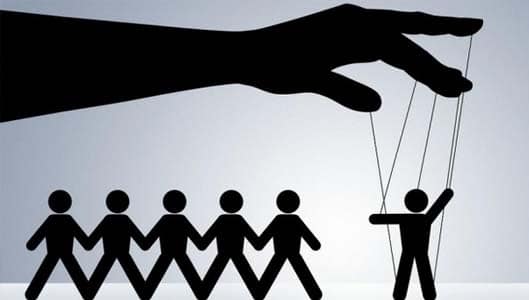
However, most cyber-scams rarely rely solely on a technical approach. Many scams incorporate a technical approach with non-technical methods, namely manipulation. This usually means manipulating a victim into compromising their own security. It is this manipulation that we refer to as social engineering.
As such, social engineering refers to any component of an online scam that isn’t technically orientated, rather relies on manipulating a victim into compromising their own security.
Sponsored Content. Continued below...
It is perhaps easiest to look at some examples of popular Internet scams and identify the social engineering component of the scam.
Some examples…
So for example, a popular Internet scam is to send a victim an email with an attachment that contains malware, with the aim of tricking the victim into opening the attachment and consequently infecting their computer. For example, the email may tell the victim that an invoice is attached. The victim, unsure as to what the invoice pertains to, may open the attachment and execute the malware.
In this instance, the development of the malware would be the technical component of the scam, and tricking the victim into opening what they think is an innocent invoice attached to the email and infecting their computer would be the social engineering aspect of the scam.
Another example could be the victim receiving an instant message from a friend on Facebook claiming that they are stuck abroad with no way to get home and urgently request the victim send them money. But in reality the Facebook friend isn’t who they seem. It was a clone account using both the same name and profile picture as one of the victim’s Facebook friends. The victim had been tricked into accepting a friend request from the impostor believing it to be their friend. The criminal cloned the account and is now looking to try and trick the victim into sending them money which they will steal.
Sponsored Content. Continued below...
In this example, the criminal used two social engineering tricks and a very limited technical approach. The Facebook cloning scam would be considered a social engineering trick since it manipulated the victim into accepting a friend request (and setting up a clone account requires very little technical knowledge) and tricking the victim into sending money using the fake “stuck abroad” story is also an example of social engineering.
These examples show how criminals can use social engineering techniques to install malware or steal money, without having to rely on any significantly technical approach.
Social engineering scams may be used alongside a technical approach or they may be used by themselves to scam victims. The best advice to avoid falling for a social engineering scheme would be to educate yourself on how such scams work by being aware of popular examples and learning how to identify the red flags.
Keep up-to-date with all the latest cybersecurity threats and our tips to stay safe online. Follow us on Facebook, Instagram and Twitter.
Continued below...
Thanks for reading! But before you go… as part of our latest series of articles on how to earn a little extra cash using the Internet (without getting scammed) we have been looking into how you can earn gift vouchers (like Amazon vouchers) using reward-per-action websites such as SwagBucks. If you are interested we even have our own sign-up code to get you started. Want to learn more? We discuss it here. (Or you can just sign-up here and use code Nonsense70SB when registering.)
Become a Facebook Supporter. For 0.99p (~$1.30) a month you can become a Facebook fan, meaning you get an optional Supporter Badge when you comment on our Facebook posts, as well as discounts on our merchandise. You can subscribe here (cancel anytime.)